Which Devices Are Most At-Risk For Cyber Attack?

Cybercriminals are no dummies. They often have a background in some sort of computer science or software development in preparation for cyber attacks. To break through codes, you need to be at least a little clever. Because they're smart, it makes sense that they find trends and ride them. For example, if they notice that a particular type of device is easier to hack into, they will likely stick to those types of attacks. Unfortunately, nearly all devices can be hacked, but some are much more common than others. Let's talk about three of the devices you're likely in close contact with that are at risk of data breach or cyber attack.
Laptops/Computers
First on our list is a household and workplace staple - laptops or computers. Think about how frequently you use a laptop for personal things outside of work, and how vital computers are to your job. There are billions of laptops or computers in the world today, each posing an opportunity for attack. Hackers will go after personal laptops to find passwords, sensitive information, access to various accounts, credit card information, location, interests, and more. Work or company laptops will usually contain all of this information and sensitive data about the company including passwords, protocols, client information, finances, IP, future plans, etc. There's a lot of valuable information on computers and cybercriminals are very aware of it. Laptops are particularly at risk if the owner uses an unsecure network/hotspots or stores data on an ill-protected cloud. Network situational awareness is key to spot weak points and catch a hacker in the act.
Smartphones
Smartphones are typically with their owners at all times. People have an arguably unhealthy attachment to their phones in some cases, and rely on it for all kinds of things. Your phone can be an alarm, a calendar, a GPS, a form of communication, a pocket-sized computer, and more. Many people store information in their phones or utilize apps like mobile wallets, mobile banking, password vaults, and more. Especially due to the prevalence of remote working, many companies provide employees with a "work phone." or subsidize mobile phone use of a personal device. As with laptops, these mobile devices tend to have at least some sensitive information in them from contacts to documents to emails and more. Cybercriminals will happily steal data from either your personal or work phone, so be sure to have the proper precautions in place. Avoid using public wifi networks (especially on work phones), require 2-Factor Authentication whenever possible, and always check on app permissions about sharing data. It's also wise to never store passwords or confidential information in your phone, and secure it with a passcode and/or facial recognition.
Point Of Sales Systems
The last device is not something you'll have at home, but it is something that any retail worker comes across. A point of sales system is where payment processing occurs. Credit card readers, checkout registers, self-checkout, etc. all fall under this umbrella. Considering that the main purpose of POS systems is to carry out transactions, they are a big target for cyber attack. A successful breach of a POS system will give the hacker access to bank information, contact information, and other valuable details about the company and every customer. We've all heard about huge retailers becoming victims of a POS breach, and thousands or millions of customers are affected. These breaches are extremely costly and have been known to ruin a store's reputation.
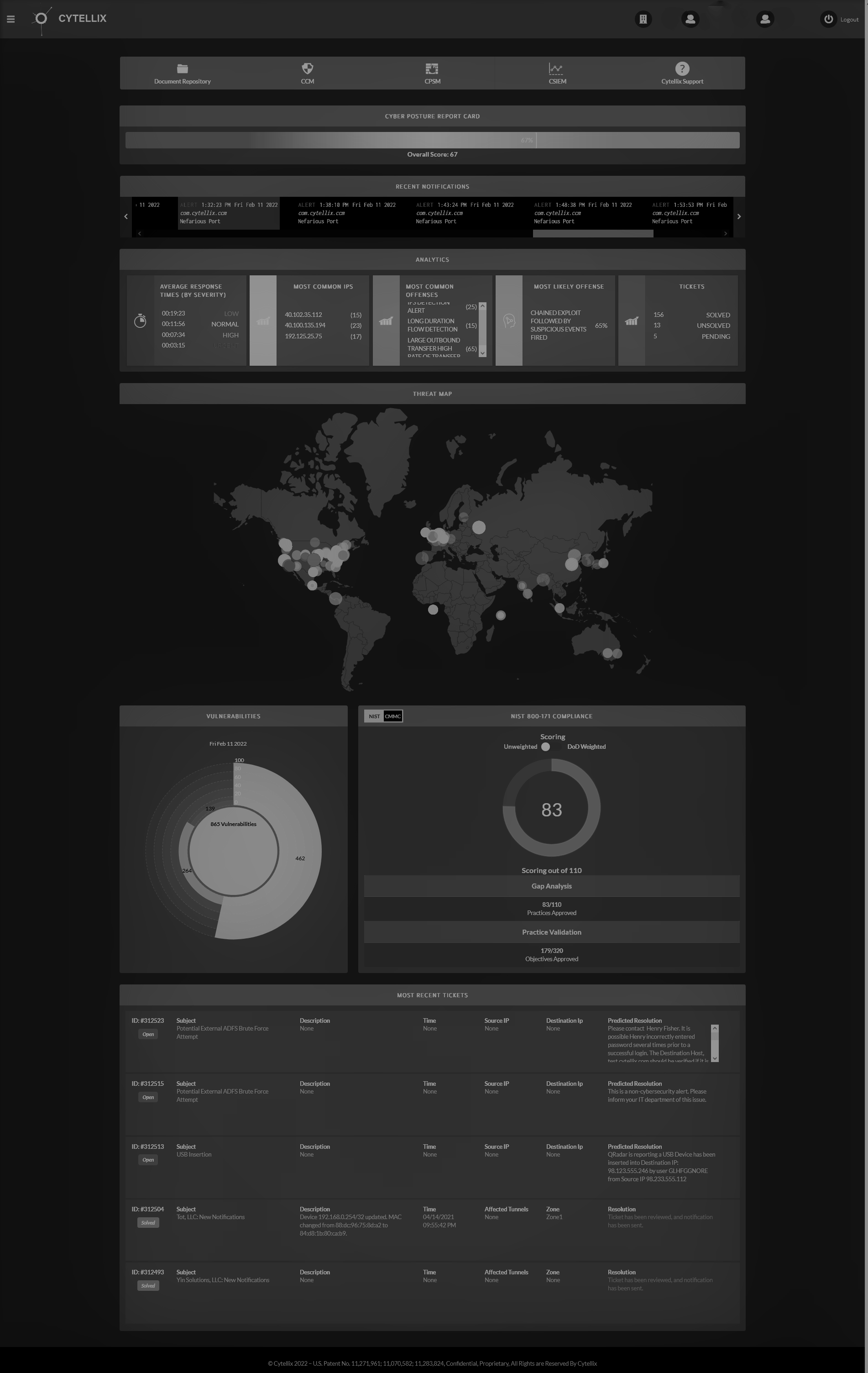
Cytellix can help your business protect any and all devices included in your IT infrastructure. We set up
continuous cybersecurity monitoring, endpoint detection and response
(EDR) that tracks all processes, detects attacks within the network as well as any endpoints (devices). Our personalized solutions will secure devices from attack, even for employees working from home. We can also secure your network, enforce the cloud, and detect any odd behavior as soon as it occurs. Speed is essential to stopping an attack, and we make it easier to react almost immediately. Learn more about Cytellix at
https://cytellix.com/ and contact us at
[email protected] to get started!

Cytellix
has expert capabilities in cybersecurity technology, risk management frameworks (RMF, NIST, CMMC, GDPR, FFIEC, ISO) and provides a complete visibility platform that supports: DoD customers, DIB Customers, DoD Supply Chain, and other highly regulated industries (Finance, Automotive, Life Science, Utilities, State and Local Government). Our technology stack includes
GRC,
EDR,
MDR,
XDR,
SIEM
as Service, 24x7 SOC, Vulnerability Management, Real-time continuous cyber monitoring, Firewall Management, and threat hunting and threat correlation.