The Top Industries at Risk For Cyber Attacks in 2022

As the world becomes increasingly digitized, more and more industries are at risk for
cyber-attacks and cyber risk in 2022 than ever before. While no industry is immune to
cybercrime, certain industries are particularly vulnerable due to the sensitive nature of their
data.
Here are the top industries at risk for cyber-attacks and who are most in need of a robust cyber
security plan:
Healthcare: Healthcare organizations are prime targets for cybercriminals due to the sensitive
nature of patient data. Hackers can exploit this data for financial gain or cause havoc by
disrupting critical medical operations.
Financial Services: Financial institutions are also attractive targets for cybercriminals due to the
large amounts of money involved. Hackers can use stolen financial data to commit fraud or
blackmail organizations for financial gain.
Retail: Retailers are often targeted by cybercriminals due to the large amounts of customer data
they collect and store. Hackers can exploit this data for identity theft or fraud or disrupt
operations by shutting down online stores through DDoS attacks.
Technology: Technology companies are increasingly targeted by cybercriminals due to their
valuable data. Hackers can exploit this data for financial gain or cause havoc by disrupting
critical operations or stealing intellectual property.
Telecommunications: Telecommunications companies are also attractive targets for
cybercriminals due to the large amounts of customer data they collect and manage. Hackers can
exploit this data for identity theft or fraud or disrupt operations by shutting down phone and
internet service.
Education: Education institutions are often targeted by cybercriminals due to the sensitive
nature of student data. Hackers can exploit this data for financial gain or cause havoc by
disrupting critical administrative operations.
Government: Government organizations are attractive targets for cybercriminals due to the
sensitive nature of government data. Hackers can exploit this data for financial gain or cause
havoc by downloading and distributing sensitive or confidential information.
How Can Companies Protect Themselves from Cyber Attacks?
As the world becomes increasingly digital, the threat of cybercrime grows. Companies must
constantly adapt to protect themselves from cyber threats with cyber preparedness 2022.
There are many ways companies can protect themselves from cybercrime. One way is to
educate employees about cyber security. Employees should be taught how to spot phishing
emails and other signs of a cyber-attack. They should also know how to keep their passwords
safe and secure.
Another way companies can protect themselves is by investing in cyber security software. This
software can help to detect and prevent cyber-attacks.
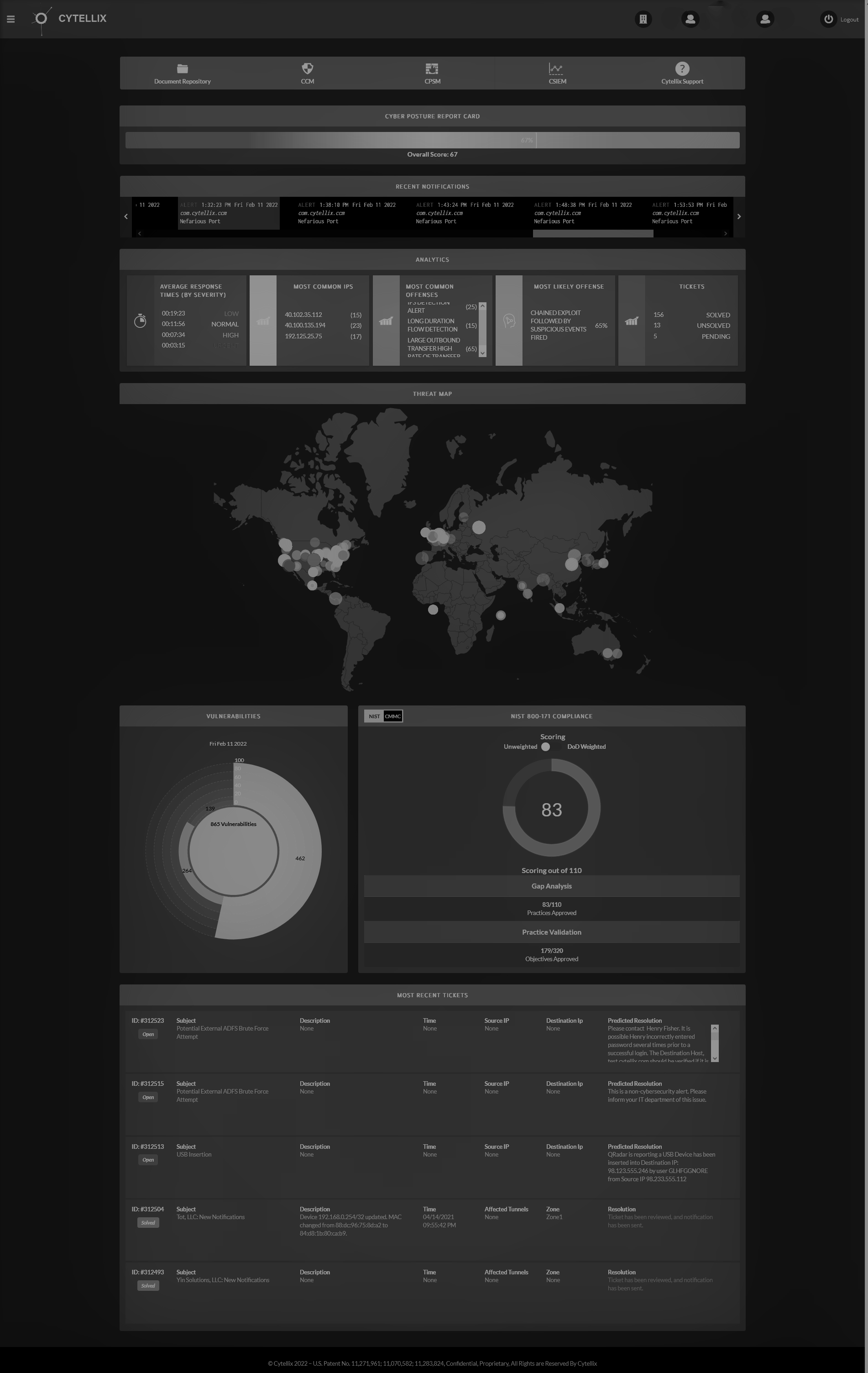
Companies like Cytellix are disrupting the industry by bringing together the full spectrum of
cybersecurity, compliance, and risk management solutions under one umbrella. Our new
software approach to cybersecurity involves a patented SaaS platform designed to correlate
compliance data, IT, cloud, and IoT assets into 24/7 advanced threat detection.
Cytellix combines the power of in-house, advanced AI capabilities and data from a third-party
security product into highly automated services that can be tailored to the needs of SMBs. We
can deliver it as a turnkey solution integrated with enterprise-owned assets and more, offering a
robust cyber security solution to large and small businesses.
Finally, companies should have a plan in place for what to do in the event of a cyber-attack. This
plan should include steps for how to contain the attack and how to recover from it.
By taking these proactive steps, companies can help protect themselves from the growing
threat of cybercrime and defend against the loss of sensitive internal and external data. Learn
more by contacting our talented team at Cytellix here.