The Hidden Aspects of Cybersecurity

It should come as no surprise that businesses are flocking to the cloud and other digital platforms to replace their outdated data management systems. The internet is a wonderful thing, and the capabilities that come with it are unmatched. Unfortunately, many businesses head online without taking the proper precautions. The internet has plenty of hackers, all of whom are looking for weak spots in data collections so they can make their move. Many business owners believe they are prepared against cyber attacks, but few are as secure as they would hope to be. Cybersecurity companies like Cytellix are here to ensure that you have no weak link, no open door, and no unprotected file floating around in the cloud. Let's take a look at some of the weakest areas of cybersecurity we often see.
Payment Processors
One of the most sought-after areas to attack are payment processors. We've all heard news stories about credit card information being stolen from retail stores, major banks, and more. Hackers will always aim to find money, so payment processors are particularly at risk of cyber attack. Hackers are adapting as technology advances, so we aren't always as safe as we think. Here at Cytellix, we are constantly looking towards the future to figure out what hackers might try next. By staying several steps ahead, we are able to safeguard any and all payment-related programs from breech. Consumers are able to make payments in many ways, several of which involve digital processes. Credit cards, debit cards, online payment, direct deposits, mobile banking, and more are all viable areas for hackers to target. It's crucial to pay extra attention to these areas to protect both company and consumer finances. When a person or business gets their credit information stolen, it is a process and a half to fix. Not to mention the lawsuits that will inevitably come if it's determined that the business did not have the proper safeguards in place. Cytellix is committed to protecting financial data at all costs, so we go the extra mile when it comes to setting up and managing cybersecurity services for payment processors.
Information Databases
When hackers aren't successful at stealing credit and banking data, they'll go for the next best thing; personal information. Identity theft is far more common than it should be. Back in the day, most identity theft cases came from someone losing an ID or being robbed. Now, with most information available somewhere in the cloud, hackers can steal thousands of identities without leaving their homes. It's shocking how frequently we put personal information online. Whenever we create online accounts, you're asked for, at the bare minimum, your name, and email address. Without the proper cybersecurity in place, your customers' valuable personal information is up for grabs. It's more important than ever to protect personal information from cyber-attacks because more and more important duties are heading online. Banking, insurance, taxes, the entirety of your smartphone's data, they're all on the cloud, and therefore all vulnerable for attack. Even though you might be asking for "general" personal information, hackers can get a lot out of it. For example, if someone can connect a name with a birthdate, cybercriminals can likely figure out their social security numbers. People of the same birth year have the same first two sections, and many websites ask for the last four digits as a login. Add them together, and you have easy access to someone's identity!
Email Systems
While email addresses can also be included in the "personal information" section, some hackers are out for them specifically. Malicious malware is sent most commonly through emails, the recipients of which could have been found through weak security spaces. In addition, emails can be hunted down by cybercriminals, only to be sold to businesses for unsolicited email lists. This is illegal but happens all the time. If hackers get into business emails, there's a chance they can then get into shared drives on Google or similar platforms. Once they're in there, the havoc they can cause has no limits. They can email clients from your accounts, change passwords, delete or corrupt documents, and more. Cytellix is fully aware that emails are valuable to cybercriminals, so we make it our mission to safeguard them. With our help, you can feel confident that internal emails and customer emails will be kept confidential as intended. Even if they don't cause too much damage, security breaches will destroy any trust that your customers have in you. It's extremely challenging to rebuild that relationship, so the best thing to do is enact cybersecurity services ASAP. Hire a team you can trust to build out and manage your cybersecurity system. With us, all emails will be safe and sound!
Manual Processes
One of the easiest things for hackers to break into is anything done manually. Human error is a business's worst nightmare, especially online. It's not wise to trust your employees to follow a rigorous protocol for tasks they often do. Odds are, something will fall through the cracks, opening a window of opportunity for cybercriminals to sneak in. We always suggest automating processes as often as possible because computers don't forget. If you need all documents to be saved in a particular folder, create an automation for it. That way, none of your valuable data can be stolen because an employee accidentally saved a Google Doc to the wrong place. The less human interaction you can make with digital tasks, the better. Of course, most human errors are completely accidental and nothing to get upset about, but an accident can result in a lot of headaches for you in the wrong situation. Cybersecurity companies will be able to look at your current processes and find weak spots vulnerable for attack. Cytellix does a thorough analysis to make sure we don't miss anything. We'll discover weaknesses caused by human error and help implement permanent solutions.
If you're ready to start working with one of the most trusted cybersecurity companies in the business, call Cytellix today! Our team of experts has been entrusted to protect some of America’s biggest companies, including the US Army, the Department of Homeland Security, the Department of Defense, and NASA. We will curate solutions specifically for you, making sure to lock up your data, so it's airtight. Call us today at (949) 215-8889 to get started.
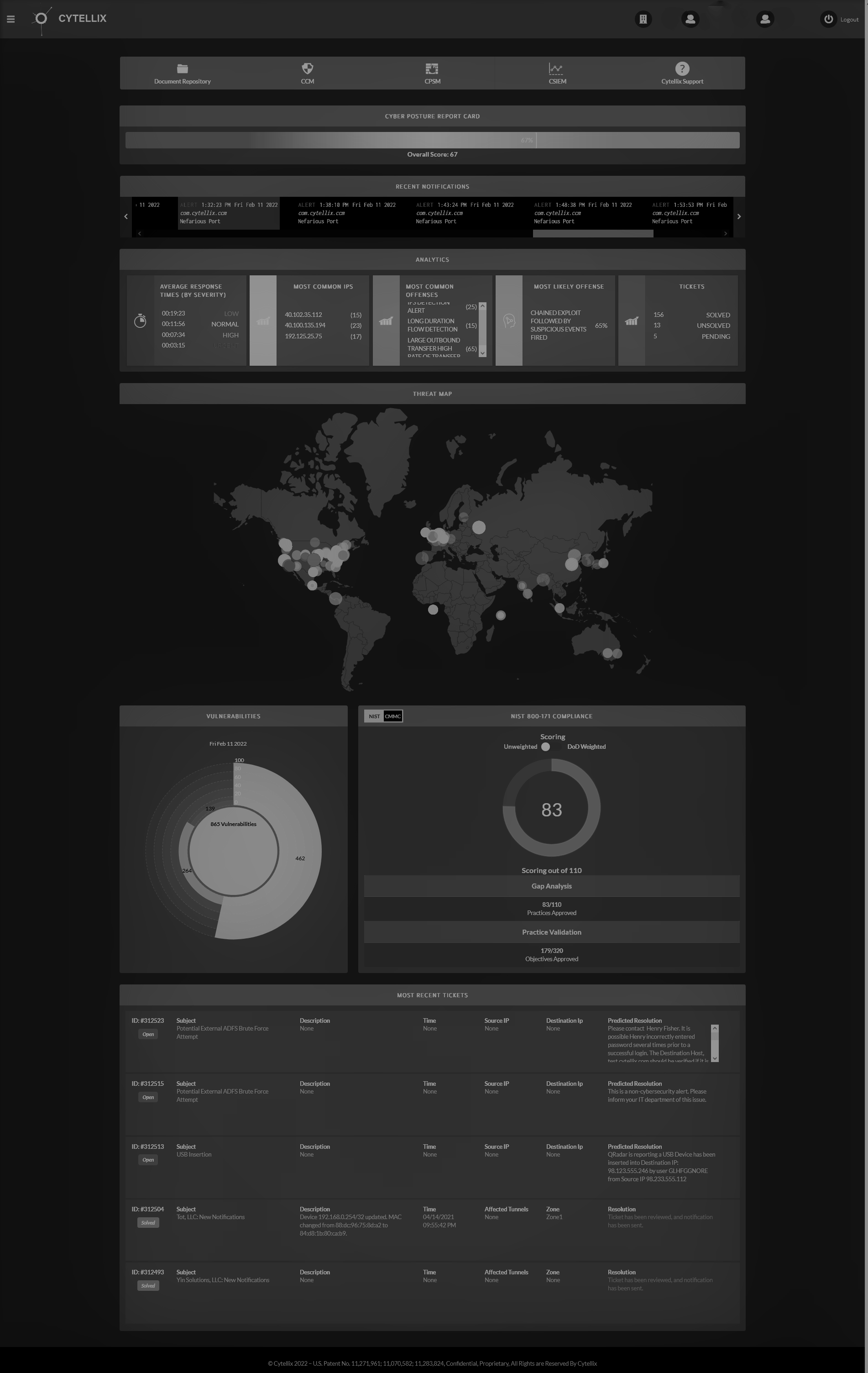
Cytellix has expert capabilities in cybersecurity technology, risk management frameworks (RMF, NIST, CMMC, GDPR, FFIEC, ISO) and provides a complete visibility platform that supports: DoD customers, DIB Customers, DoD Supply Chain, and other highly regulated industries (Finance, Automotive, Utilities, State and Local Government). Our technology stack includes SIEM as Service, 24x7 SOC, Vulnerability Management, Real-time continuous cyber monitoring, Firewall Management, and threat hunting and threat correlation.
The post The Hidden Aspects of Cybersecurity appeared first on Cytellix.