Solve Problems Before They Arise With Network Situational Awareness
As a business in 2022, you can't escape the many uses of the internet and networks. Cloud-based storage, applications, and processing have completely changed the game, making completing tasks easier, faster, and more efficient. You would be hard-pressed to find any successful company that does not use some form of digital solution. While most networks are identified as "secured," do you have all the protection you need against cybercriminals? The best way to avoid problems is to catch them before they start. You can identify weaknesses in your network with Network Situational Awareness and continuous cybersecurity monitoring. Here's what this revolutionary cybersecurity solution can do for you and a few things it will help you watch for.
What is Network Situational Awareness?
Network Situational Awareness is precisely as it sounds; being aware of the state of the network your business operates on. Networks are spaces that allow communication between multiple devices. Data is collected and stored in the network and is only accessible to those devices within it. Companies or any business that deals with a lot of sensitive information turn to private networks to keep this data safe. These networks are secured with passwords, pin codes, firewalls, and more security checks to prevent those outside the company from gaining access. Like all other aspects of digital technology and cybersecurity, even the most secure network can have weak spots that put you at risk for a cyberattack. Network Situational Awareness is a system of continuous cybersecurity monitoring that can keep an eye on the network as a whole to identify and flag problems. By staying aware of your network’s status, you can stay one step ahead of hackers to keep valuable information safe. Network Situational Awareness is very involved because of all the moving parts in a network. With the help of cybersecurity experts like Cytellix, you can easily monitor the goings-on from one place.
Who Needs Network Situational Awareness?
Any business that uses a network would greatly benefit from Network Situational Awareness. Leaders in the company need to be able to look at how the network is performing currently versus how it is expected to perform. You need to look at the past, present, and future state of the system to determine how you're doing security-wise. Many people erroneously believe that they are secured enough that there's no reason for concern. The fact of the matter is that the more the network changes, the more likely something is to fall through the cracks. When you're managing fifty or hundreds to thousands of devices on one network, you need to ensure that every possible security measure is being taken. Basically, the more you rely on your company network to do daily tasks, the more important it is to have Network Situational Awareness. Cybersecurity monitoring software and processes can proactively scan every inch of the network to detect problems that would be missed by traditional networking software. Find weak spots before hackers do and avoid data breaches, external attacks, and more.
How Can Cytellix Help?
Cytellix offers state-of-the-art Network Situational Awareness solutions to businesses across all industries. Our program has several overall goals that will protect you, your company, and your clients' information. These goals include:
- Proactively identify and monitor 100% of network connections and devices.
- Understand all aspects of the network environment — physical, mobile, virtualized, IoT, and cloud (private, public, and hybrid)
- Expose potential problems, such as unplanned Internet connections, unmanaged devices, and unsecured ports
- Monitor in real-time for instant visibility and immediate response
- Alert by severity for threats, leaks, and nefarious activity
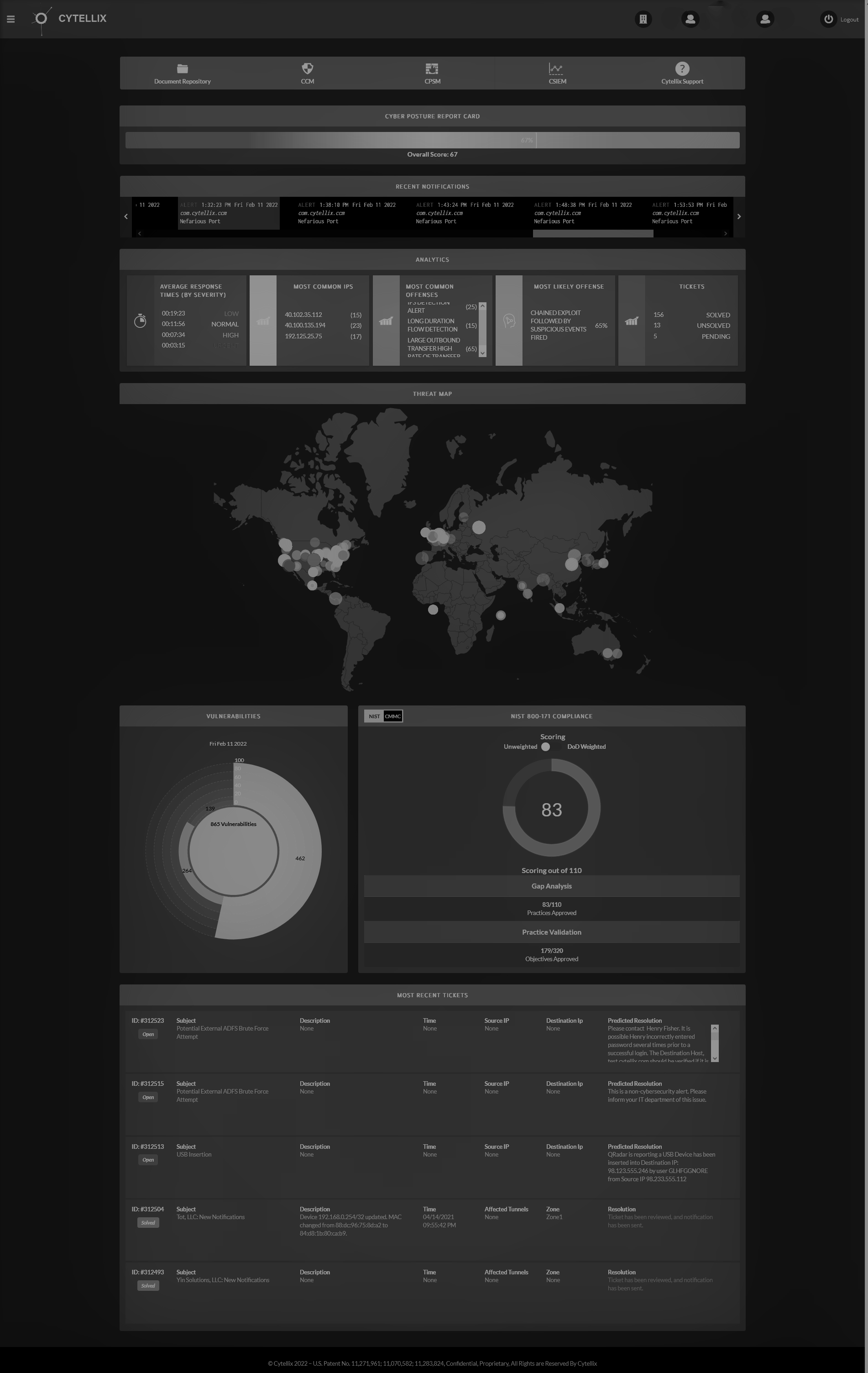
Cytellix created a continuous cybersecurity monitoring system especially to keep an eye on your network. Running in an always-on mode, Cytellix Continuous Monitoring delivers next-generation network discovery, leak path detection, visualization, and analytics to provide network situational awareness — including awareness of your organization’s presence in private, public, and hybrid clouds. Our cybersecurity continuous monitoring has saved clients from catastrophic cyberattacks, data breaches, and network takeovers. We can create personalized solutions for any size business. We even help multi-location businesses keep data secure in company-wide networks or clouds. When you work with Cytellix, you can feel confident that you will be alerted to any cyber or network weaknesses immediately and receive implementation plans to fix said issue.
In addition to Cytellix Continuous Monitoring for Network Situational Awareness, we also offer custom, high-tech cybersecurity solutions including Risk Management, SIEM as a service, the patent pending Cytellix Cyber Watch Portal, and more. Our turnkey solutions will keep you several steps ahead of cyber criminals so that you can spend less time worrying about your data and more time using it to better your business. Reach out to our team today to get started down the path to improved cybersecurity. Want to get more information? Contact us here today.
Cytellix has expert capabilities in cybersecurity technology, risk management frameworks (RMF, NIST, CMMC, GDPR, FFIEC, ISO) and provides a complete visibility platform that supports: DoD customers, DIB Customers, DoD Supply Chain, and other highly regulated industries (Finance, Automotive, Utilities, State and Local Government). Our technology stack includes SIEM as Service, 24x7 SOC, Vulnerability Management, Real-time continuous cyber monitoring, Firewall Management, and threat hunting and threat correlation.