NIST SP 800-171 & CMMC Interim Rule Effective November 30, 2020
NIST SP 800-171 & CMMC Interim Rule
Department of Defense’s Interim Rule Effective November 30, 2020

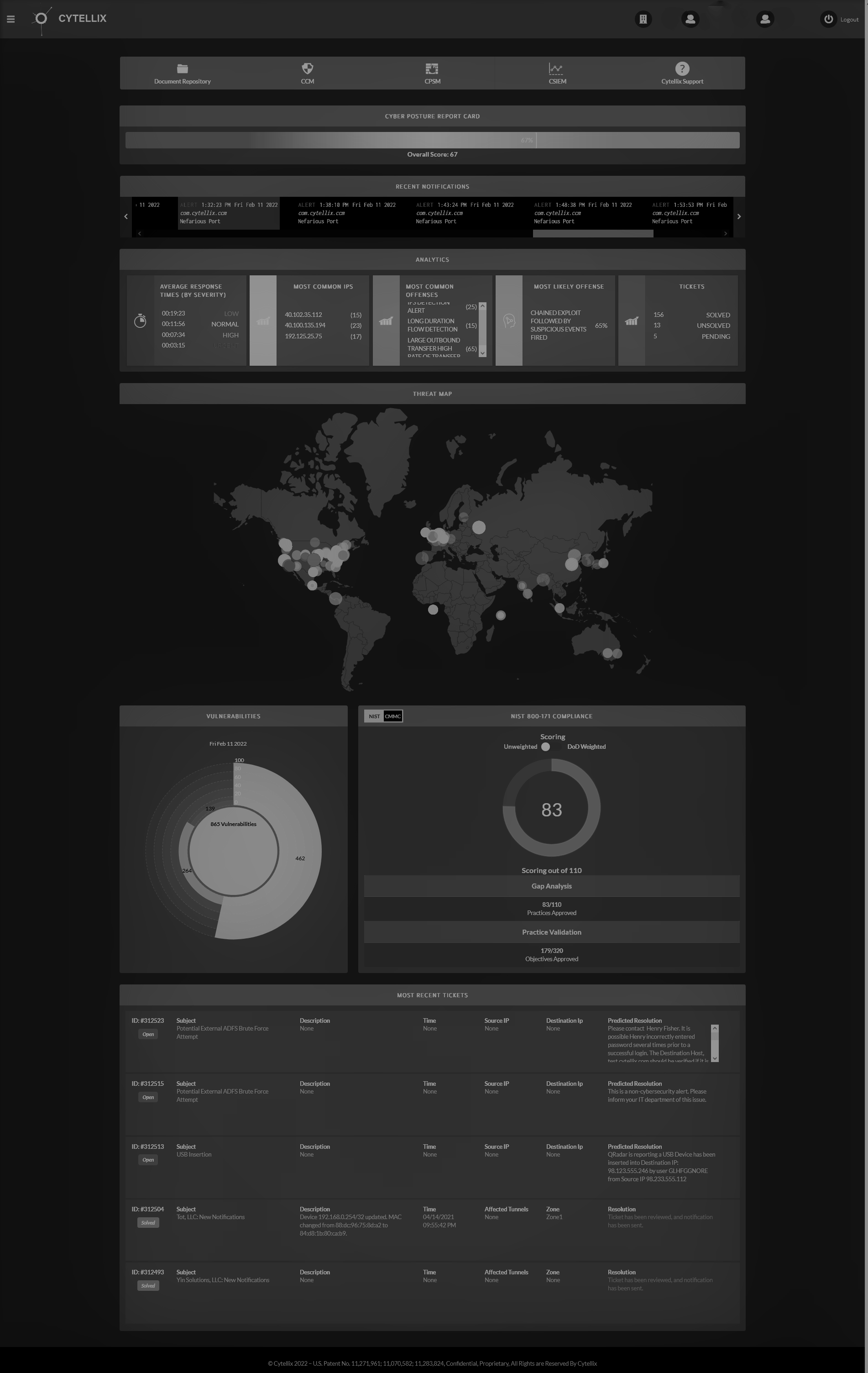
On September 29, 2020, the Department of Defense (DoD) released an interim rule that requires all suppliers to have a current assessment on record in the Government Data Base SPRS (Supplier Performance Risk System). This applies to organizations who do not provide commercial off-the-shelf (COTS) items. The rule focuses on DoD’s increased requirements for confirming that contractors are currently in compliance with and have implemented all 110 security controls in National Institute of Standards and Technology (NIST) Special Publication (SP) 800-171. There have been a number of cases of high-profile cyber incidents involving defense programs that requires suppliers in the Defense Industrial Base (DIB) proof of compliance and/or proof of advancing compliance. CMMC is doing a phased to rollout that is expected to take up to 5-years. Until the complete roll-out, the interim rule is in effect.
DoD has interpreted “implement” to mean that a contractor must create a System Security Plan that explains whether the contractor is in compliance with each of the 110 security controls and a Plan of Action and Milestones (POA&M) that describes how and when the contractor will attain full compliance for any control that is incomplete. Incomplete controls are any control that there is no proof, evidence or artifact that can verify the control is adequately implemented.
What does this mean to suppliers within the DoD supply chain? The DoD is checking SPRS and any supplier on a new contract must have a current assessment ”fresher than 3-years old” backed by a gap analysis, System Security Plan (SSP) and Plan of Action and Milestones (POA&M) with actionable plans to become in compliant quickly. The DoD will perform Assessments (audits) of the information provided in SPRS for suppliers they consider are handling sensitive information that may be critical to the program. Flow-downs to subcontractors, for non-COTS suppliers, must be enforced and those suppliers must post in SPRS as well. A contractor may not award a subcontract unless the supplier is in SPRS with a current assessment, and validation of an accompanying POA&M and SSP.
Procedures for Contract Awards:
- Contracting officer shall verify the summary level score of a current NIST SP 800-171 Assessment, for each covered contractor information system that is relevant to an offer, contract, task order, or delivery order posted in SPRS. Prior to:
- Awarding contracts, task orders or delivery order to an offeror or contractor that is required to implement NIST SP 800-171 in accordance with DFARS clause 252.204.7012: or
- Exercising an option period or extending the period of performance of a contract, task order or delivery order with a contractor that is required to implement NIST SP 800-171 in accordance with DFARS clause 252.204.7012.
How long you do you have? November 30, 2020 or within 30-days of your completed assessment to post in SPRS. After November 30, 2020, option-year exercises of an existing contract, require this as well. The key message prior to CMMC certification is that suppliers must be prepared for an audit and the self-assessment / attestation of compliance will be tested for accuracy. Act sooner than later as preparation and proof of compliance and have actionable remediation steps. This is not a simple paperwork exercise!
Assessment requirements (summary)
- Assessment is a review of SSP associated with the covered contractor information system(s)
- Conducted leveraging the DoD Assessment Methodology
- Preparation for a DoD Assessment
- Review Assessment
- Artifact review to verify documentation and implementation per the SSP
As with previous communications, falsifying records can result in different outcomes depending on the breach or loss of Controlled Unclassified Information (CUI). These include: Loss of contract, corrective action report, punitive damages to criminal prosecution. Remember compliance with NIST SP 800-171 and the future certification under CMMC, requires having all your documentation, technology, vulnerabilities and cyber-monitoring in place. You must have proof of compliance, manage the CUI access, understand threats, leaks, know when your under attack, be able to define if information has leaked from your company, identify the severity of a breach and be able to notify your prime contractor and the DoD of any breach within the notification period. In direct terms, understand your vulnerabilities, monitor for attacks, have control of all logs and external / internal threats and have an actionable model to stop data leakage from occurring in all areas of your business. Get help, be precise, and work with subject matter experts, real cybersecurity is above the common IT services paygrade.
If you have any questions, please reach out to our Team –[email protected]