DoD Supply Chain – THE DEADLINE DELAY IS OVER

The deadline for the supply chain to meet compliance with NIST SP 800-171 under Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012 was December 31, 2017. As we are all aware, the enforcement and teeth of this deadline was deferred until NOW. By the end of August 2018, all contractors who have been awarded contracts to provide products or services which requires the use of Controlled Unclassified Information (CUI), will be put on notice that enforcement will begin with the new government fiscal year starting October 1, 2018. The obligation of proof is placed upon the supplier, their suppliers and their suppliers.
What does this mean for the supply chain under these contracts? Audits will begin on October 1, 2018 for proof of compliance. The two forms of remedies for failing the audits include a Corrective Action Reports (CAR) and/or loss of contract. The end of the “grace period” has come to an end as well as the request for waivers.
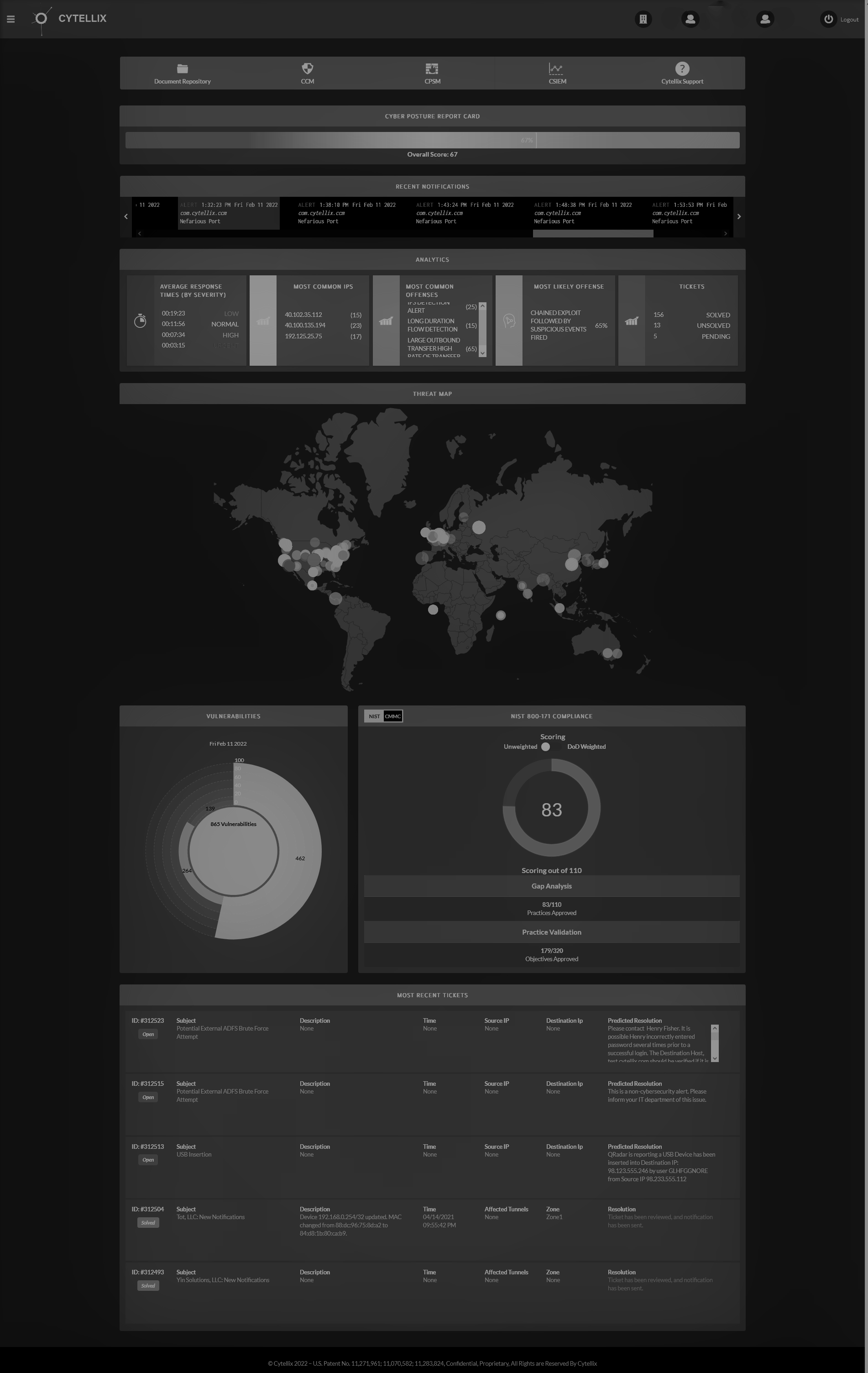
What will occur in the audit is not merely a documentation exercise. Many consultants provided support that includes preparing documentation and policies; however, they have not done what is necessary to fulfil the Cyber requirements under these contracts. The obligation and requirements to be compliant is not a paperwork exercise. The complete cybersecurity assessment is an aggregation of technology, networking, security, situational awareness, vulnerability awareness, policies, procedures, and the cyber event reporting obligation.
As mentioned above, the cyber-compliance requirements must be backed up by proof. Proof is defined differently by different people, but, in the end, the burden is on the suppliers to have knowledge, evidence, and awareness of all the cyber controls, implementation, vulnerabilities, real-time cyber events and processes around each control, vs a checklist.
Below are the minimum requirements:
- Self-Attestation of the contract obligations for compliance – Attesting to compliance
2. System Security Plan with the following provable elements (updated periodically)
a. System Boundaries – Identify the network map, connections and segmentations initially and through the life of the contract
b. System Environments of Operations - Operating Environment where CUI is stored.
c. How are the security requirements implemented – Both policy, actual evidence and proof of the security requirements are active in real-time.
d. Relationships with or connections to other systems – Real-time situational awareness of connections and system profile information.
3. Plan of Action & Milestones – the detailed plan of cyber gaps and remediation's necessary and updated to show continuous improvements.
4. Incident Response Plan – An approved process defined by the DoD for reporting incidents within 72-hours of the event. The 72-hour time limit is Not negotiable.
5. Be prepared to prove your cyber resiliency with implemented “adequate” cybersecurity controls, cyber event monitoring and processes. If you cannot, your business is at risk from cyber criminals and loss of federal contracts
The time is now to act, and both prepare for compliance and become cyber prepared. The reality is your company is listed in multiple data base directories that you potentially hold CUI – you are a high risk of being attacked. When you are attacked the nation’s, security is at risk. Become cyber prepared and protect the nation, your business and your employees.