Defining CUI – Controlled Unclassified Information for the Manufacturing Segment
The definition of CUI, or Controlled Unclassified Information, by the Department of Defense is challenging for most small and medium manufactures to grapple. The NIST Frameworks for Cybersecurity SP800-171 have defined CUI under the context of “Protecting Controlled Unclassified Information (CUI) in Nonfederal Information Systems and Organizations.” The security requirements of 800-171 apply to all components of nonfederal systems and organizations that process, store or transmit CUI, or that provide security protection for such components. I will walk through the various standards and definitions to highlight the specifics that affect our manufacturers who need to meet compliance with the NIST cybersecurity guidelines. As this background currently applies to commercial manufacturing under DOD contracts, the guidance and definitions are in either draft or consideration for other verticals, including financial services, healthcare, food safety, automotive and other related verticals.
What is CUI? According to the National Archives, “Only information that requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and government-wide policies may be CUI. this excludes all information that is classified under Executive Order 13526 of December 29, 2009, or the atomic Energy act, as amended.” In commercial manufacturing, this would be anything other than COTS (Commercial Off-The-Shelf) and includes modified COTS products. The summary and extension is to any organization that provides a product or solution that is designed for government or modified for government, the information associated with such would be considered CUI. CUI is: (i) provided to the contractor by or on behalf of DoD in connection with the performance of the contract; or (ii) collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract; falls in any of the following categories: (i) controlled technical information, (ii) critical information, (iii) export control (iv), any other information, marked or otherwise identified in the contract, that requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and government-wide policies (e.g., privacy, proprietary business information).
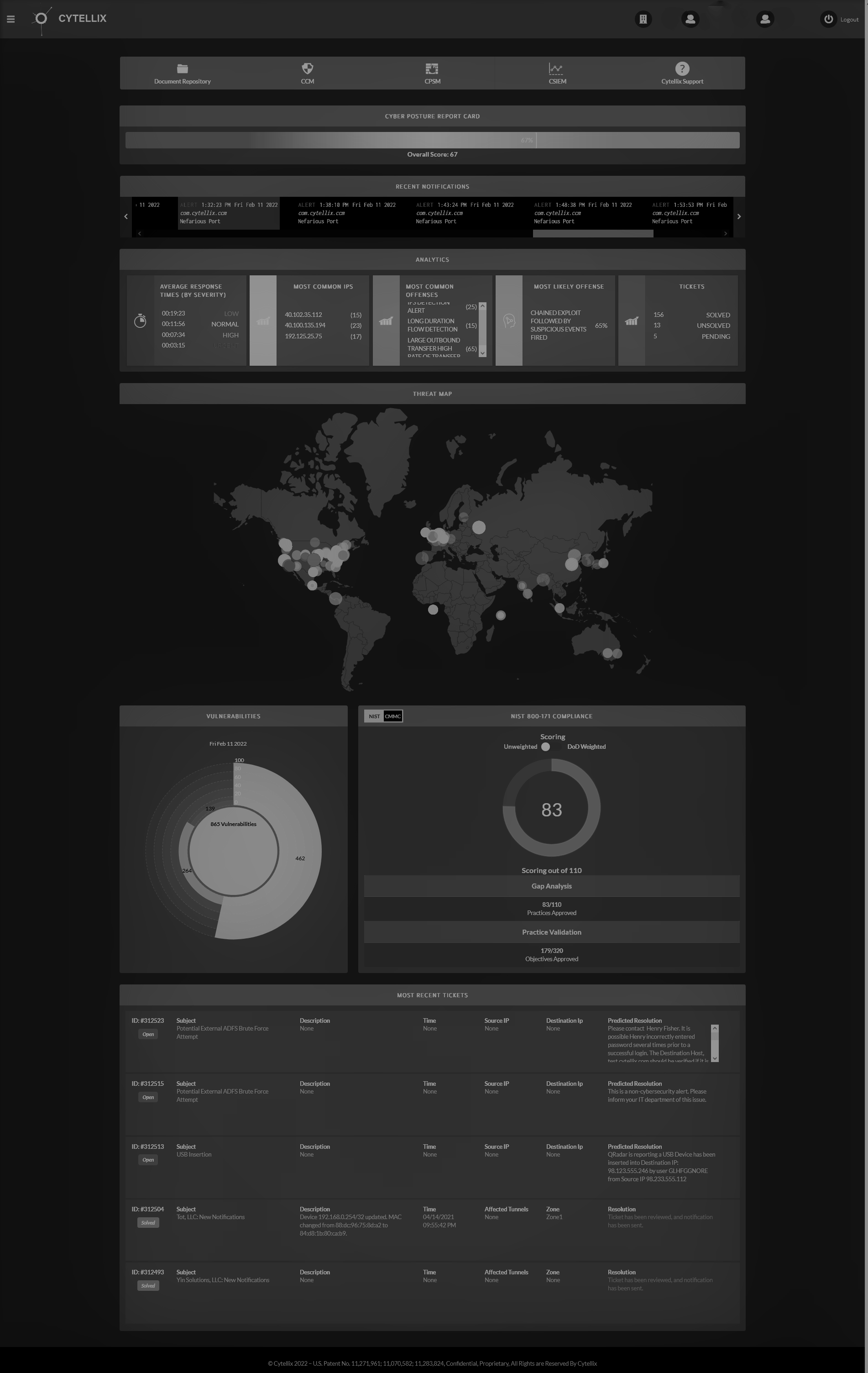
How do you protect CUI? Provide adequate security to safeguard covered defense information that resides on or is transiting through a contractor’s internal information system or network. Adequate security is defined as implementation of NIST SP800-171 that include the 14-controls for cybersecurity and is required by 12/31/2017. Compliance with 800-171 is considered 100 percent complete with any waivers or deviations approved by the DOD CIO. An organization can demonstrate through Plans of Action (POAM) and System Security Plans (SSPs) that they are in-progress as part of a contractor’s risk management decision of CUI protection by their supply chain.
Cyber incidents are another component of the compliance or CUI program. A cyber incident is an action(s) taken through the use of computer networks that results in a compromise or an actual or potentially adverse effect on an information system and/or the information residing therein. “Compromise” means disclosure of information to unauthorized persons, or a violation of the security policy of a system, in which unauthorized intentional or unintentional disclosure, modification, destruction, or loss of an object, or the copying of information to unauthorized media may have occurred.
What steps must be taken if a cyber incident occurs? Affected parties must:
- Review contractor network(s) for evidence of compromise of covered defense information using contractor’s available tools including, but not limited to, identifying compromised computers, servers, specific data and user accounts.
- Identify covered defense information that may have been affected in the cyber incident.
- According to DFARS Clause 252.204-7013(c)(1), they must rapidly report (within 72 hours of the discovery of an incident) directly to DoD and the subcontractors need to provide the incident report number, automatically assigned by DoD, to the prime Contractor (or next higher-tier subcontractor) as soon as is practical.
The need for critical infrastructure and supply chain cyber improvement has now become a requirement. We are seeing more and more cyberattacks on this market segment that result in the rapid and “unknown” theft of intellectual property, data and designs. Copied and counterfeit products, parts and infrastructure cause damage to the US economy.
The extension of the standards to other vertical markets is not a question of “if,” but a question of “when.” Prepare to adopt the NIST framework in every vertical market as a measurable, identifiable and comprehensive approach to understanding cyber posture of any organization.
*Nationalarchives.gov
**DFARS Clause 252.204-7012(c)(1)