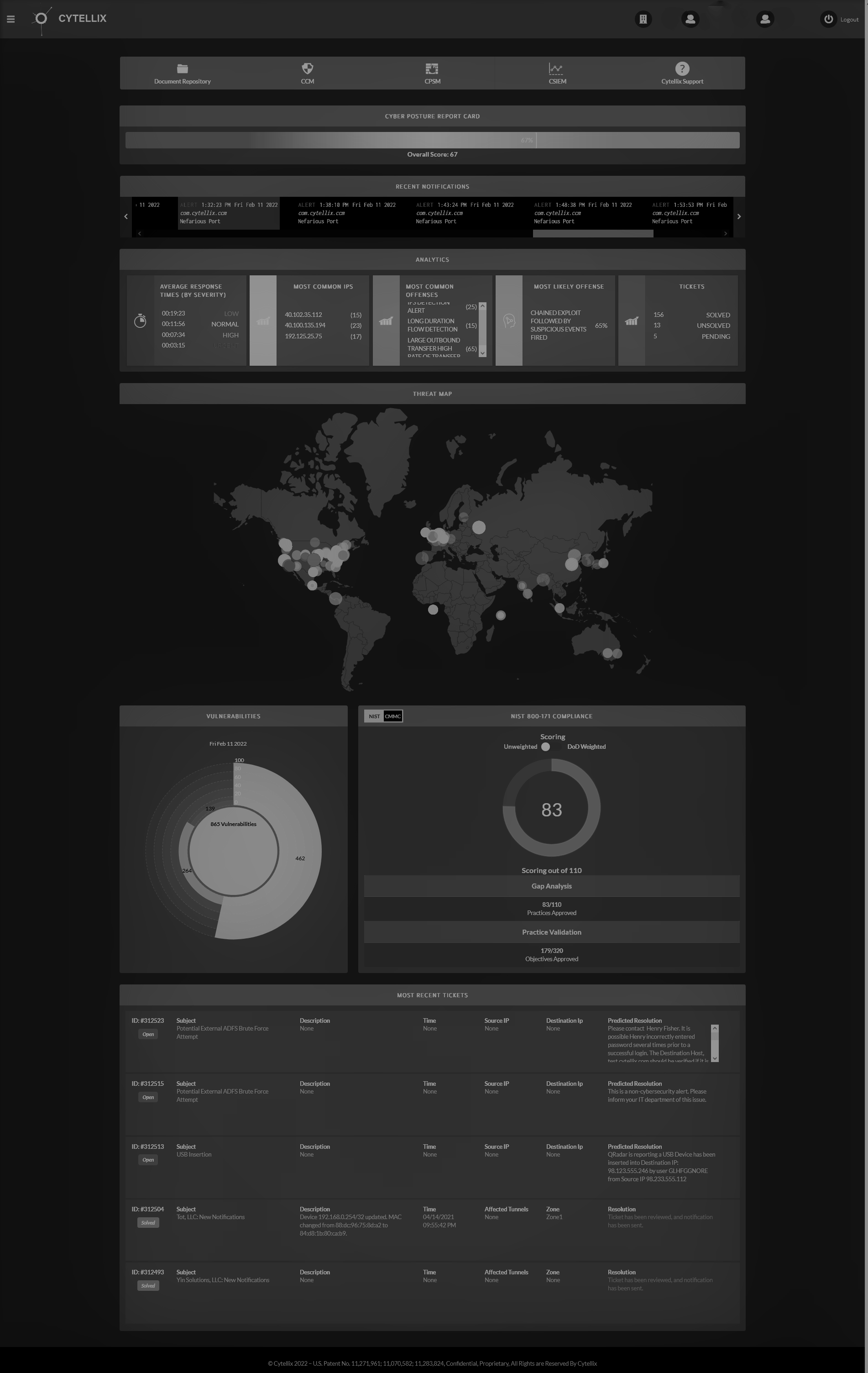
The Department of Defense (DoD) has formally presented the CMMC regulation for official evaluation, marking the start of its journey toward formal announcement. Every regulation proposed by the executive branch, including this one, undergoes scrutiny by OIRA, a division of the Office of Management and Budget (OMB). The significance of this step is that the previously mentioned "delays" in the CMMC process were due to the time taken for the DoD to forward the rule to OIRA. With this action now taken, the subsequent stages of the rulemaking procedure are underway. Nevertheless, due to the intricate nature of federal rulemaking, several more stages need to be navigated before the CMMC becomes a part of contracts. The following scenarios should be considered for preparation for compliance and certification for the Defense Industrial Base (DIB). Scenario 1: Proposed Rule Submission to OIRA: The Department of Defense (DoD) has officially submitted the CMMC rule for regulatory review to the Office of Information and Regulatory Affairs (OIRA). Review and Publication: After OIRA's review, which takes an average of 66 business days, the CMMC rule is expected to be published in late October 2023. Public Comment Period: A standard 60-day public comment period will follow, ending in December 2023. Finalization: The CMMC rule will be published as a "proposed rule", which means it will only become effective after the agency responds to public comments in a final rule. Based on historical data, the average time for DoD proposed rules to be published as final rules is 333 business days. This means the CMMC final rule is expected between February and April 2025 . Phased Roll-Out: The DoD plans a 3-year phased roll-out for CMMC contract clauses. Assuming the final rule is published in Q1 2025, all relevant DoD contracts will contain CMMC by 2028. Scenario 2: Interim Final Rule Immediate Effectiveness : If the CMMC rule is published as an "interim final rule", it will be effective before the agency responds to public comments . This means the rule would be in effect and appear in contracts in Q1 2024 . Rarity of Interim Final Rules: Such rules are rare and bypass the usual democratic process of "notice and comment" rulemaking. They are typically granted in urgent situations, like the need to enhance national security. So when should you start preparing? Before we start with the background and changes, let’s talk about the "Big Elephant” in the room. Clearly, the updated compliance and certification process developed by the DoD and the non-profit organization liaisons has been long overdue with a lot of anticipated deadlines that never materialized. And with the latest announcements it does seem to be mildly reminiscent of the movie comedy and colloquial meaning of Groundhog Day. Since the Library of Congress selected the film for preservation in the National Film Registry I found humor in relativity, not cynicism. Opinion: This is different and the information we have in the DoD supply chain must be protected from our adversaries. This is a serious issue and needs clear and precise guidelines as the supply chain will not spend money on the protection of the information that protects national security unless they must as it is deemed as a complex undertaking. That’s an unfortunate reality. We have seen the start and restart of the cyber programs for DoD for the past 5-years, what makes this different? The implementation of the CMMC rule in contracts will be phased in over a period of 3 years, with all relevant DoD Defense Industrial Base (DIB) contracts containing CMMC by 2028. For a company with 50-100 employees operating in the DoD supply chain, it takes an average of 12-18 months to prepare for assessment and audit for eventual certification, with certification being the ultimate requirement for compliance. Therefore, the time is now to start the process if you plan to hold government contracts in 2024/2025. There are also varied flow down requirements that need to also be taken into consideration. Understanding Plan of Action and Milestones (POAM) There is now the ability to present interim status vs 100% compliance as we have with the current DFARS and NIST requirements. These interim reports can be handled in the traditional manner by presenting a Plan of Action and Milestones (POAM) that have a less than 180-day completion date for allowed baseline gaps. Unallowed gaps will have a “No POAM” designation and need to be implemented. If you have any doubts, work with a highly skilled 3 rd party who has expertise in these standards and a track record of enabling comprehensive successful standards-based cyber programs. The information presented by the suppliers in POAM’s or claiming 100% compliance will be evaluated and can and will likely trigger audits if certain high-level cyber controls are not met or the 100% compliance score creates suspicion of a false claim. Be careful to present accurate and validated information. So, what does this all mean? You must be compliant with DFARS clause 252.204.7012 and NIST 800-171 today. This is a requirement of your current contracts, and the False Claims Act applies to all cyber compliance representations. If you are not compliant, you could be subject to civil penalties and criminal charges. You need to start preparing for CMMC 2.0 today. The deadline for the final rule is 18 months from now, and it will take an average company in the DoD supply chain 12-18 months to become assessment ready. Waiting is not an option. Waiting is a bad idea. Why you ask? It is very clear that most suppliers and Small and Medium Businesses are not cyber ready and nowhere near compliant with any cyber framework. The timeframe for a typical business to understand, develop and implement full compliance is more than 1-year assuming they have the skills and personnel to complete the objectives. CMMC 2.0 clearly aligns with DFARS and NIST, so it is the best way to protect your organization's sensitive data. Don't delay, start preparing today! *If you have any questions, please reach out to our experts –
[email protected]