COVID-19 Remote Working Leveraging NIST/CMMC Cyber Guidance
COVID-19 Remote Working Leveraging NIST/CMMC Cyber Guidance

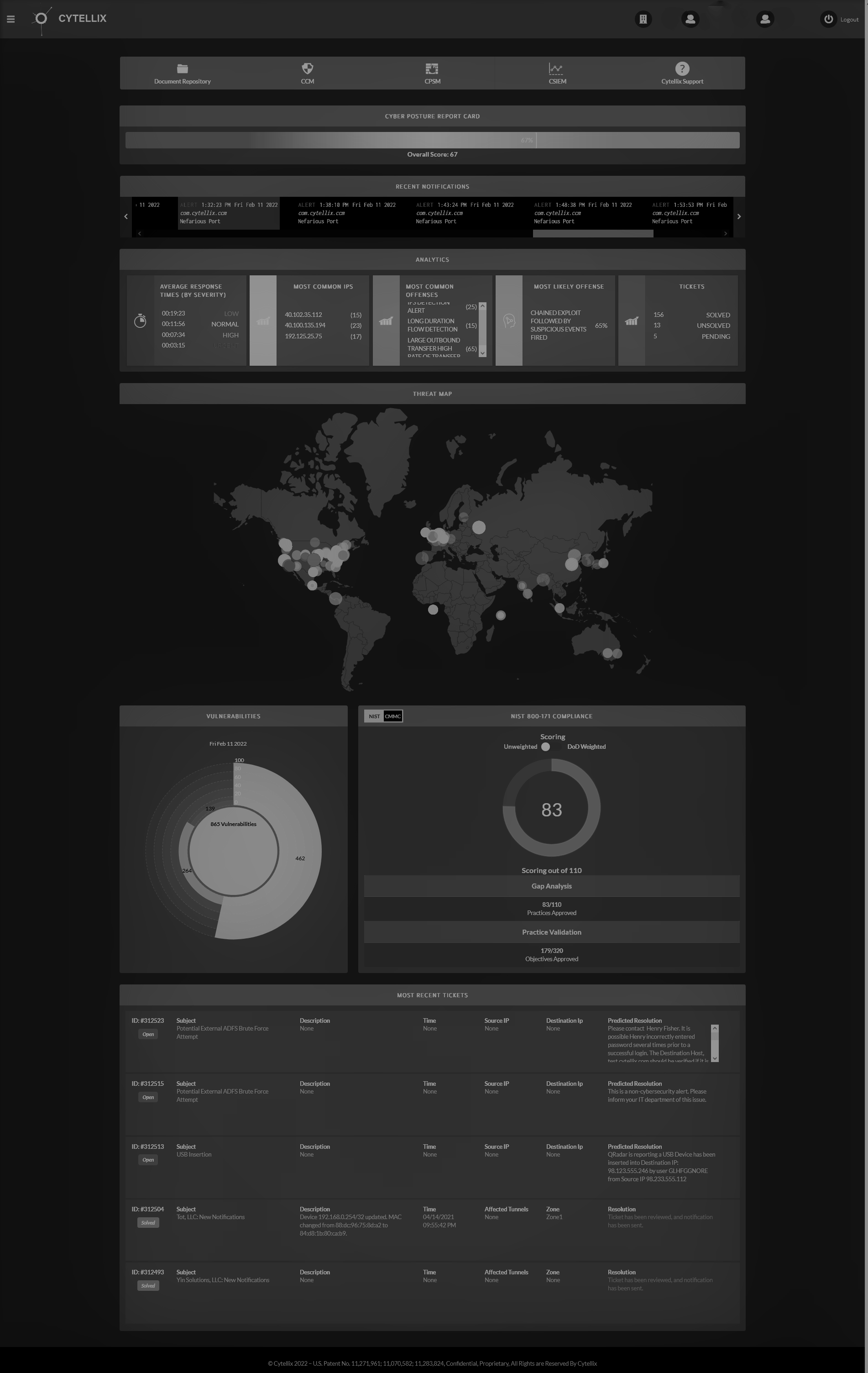
NIST SP800-171 and CMMC best practices enclosed provide guidance to meet compliance requirements for remote working. The talented Cytellix Corporation cyber analysts prepared the following guidance. Please take advantage of this valuable set of insights to support your organizations needs for safe remote working and cyber compliance: "Its just good cyber hygiene"
Remote Work Cybersecurity Concerns
Working from home, along with other forms of remote work, can present many challenges for organizations trying to balance security concerns with the ability to operate as effectively as possible. The NIST SP 800-171 and now CMMC standards for cybersecurity define several best practices that help to secure access to systems and data, as well as the practices needed to continue business operations by remote workers.
Practices directly related to NIST SP 800-171/CMMC (the Cybersecurity Maturity Model Certification)
Secure connections to your environment from the outside
If employees require access to systems and/or data that reside at company facilities, maintaining the security of those connections is a top priority. Remote access extends the security control enabled on-premise to remotely connected systems, but different risks need to be mitigated with expanded connectivity.
- Use VPN/HTTPS to ensure connections and communications are protected SC.3.190 – Protect the authenticity of communications sessions.
- Ensure secure authentication methods for remote access connections and enforce strong encryption for transmitting data in remote access sessions AC.3.014 – Employ cryptographic mechanisms to protect the confidentiality of remote access sessions.
- Ensure VPN connection are configured to prevent split tunneling SC.3.184 – Prevent remote devices from simultaneously establishing non-remote connections with organizational systems and communicating via some other connection to resources in external networks (i.e., split tunneling).
- Ensure network connections are terminated once communication sessions end SC.3.186 – Terminate network connections associated with communications sessions at the end of the sessions or after a defined period of inactivity.
- Enforce security for remote access sessions and monitor remote access activity AC.2.013 - Monitor and control remote access sessions.
- Use a limited number of remote access control points (entry points into the environment) AC.3.014 – Route remote access via managed access control points.
- Require multi-factor authentication for all remote access IA.3.083 – Use multifactor authentication for local and network access to privileged accounts and for network access to non-privileged accounts.
Consider and authorize high-privileged remote access to both systems and data, following the least privilege principle.
High privileged access carries inherent risks that are amplified when extended over remote access. With unrestricted high-privilege access, a compromise of a system admin account may result in unchecked lateral movement of attacks by external threats in your environment. Limiting the scope of high-privileged access as much as is feasible, for both systems and data, helps to mitigate the risks related to compromise of high-privilege accounts.
- Review authorization for access to systems from remote locations AC.3.021 – Authorize remote execution of privileged commands and remote access to security-relevant information.
- Review authorization for access to sensitive data from remote locations AC.3.021 – Authorize remote execution of privileged commands and remote access to security-relevant information.
Ensure procedures are in place for the handling of sensitive data (controlled unclassified information, federal contract information, personal identifiable information, and other confidential/proprietary data)
Measures for secure handling of sensitive data should cover operations and activities both inside and outside controlled facilities and spaces. Certain types of data have more directed requirements for handling (e.g. CUI/FCI), but organizations should determine how other types of sensitive data should be handled—from receiving and processing, to storage, and disposal/destruction.
- Establish CUI handling procedures for alternate work sites (including teleworking). Consider behaviors such as where/how data is stored, how physical media with sensitive information is stored and disposed of, and PE.3.136 – Enforce safeguarding measures for CUI at alternate work sites. MP.2.119 – Protect (i.e., physically control and securely store) system media containing CUI, both paper and digital.
- Control CUI/sensitive information flows—what systems that information is allowed to move between, and how that data moves. AC.2.016 – Control the flow of CUI in accordance with approved authorizations.
Establish and enforce guidelines for system and device security
The systems used for remote work, whether company provided or BYOD, should have a level of security enforcement to mitigate risks from unauthorized installations and working in unsecured spaces and networks. Also, with corporate provided systems seeing more general use in remote work scenarios, control over physical media use help reduce risk of malware attacks and data breaches.
- Control the use of external systems (including BYOD). Remote workers should use approved methods of collaborating, especially when dealing with sensitive information. Ensure cloud and SaaS based collaboration tools are functional while enforcing security. AC.1.003 – Verify and control/limit connections to and use of external information systems.
- Use mobile device management to control/manage laptops and smart phones/tablets. AC.3.020 – Control connection of mobile devices.
- Ensure inactivity screen-lock is enabled AC.2.010 – Use session lock with pattern-hiding displays to prevent access and viewing of data after a period of inactivity.
- Ensure use of portable storage devices is controlled AC.2.006 – Limit use of portable storage devices on external systems. MP.2.121 – Control the use of removable media on system components.
- Prevent the remote activation of collaborative devices (webcams, microphones) SC.2.178 – Prohibit remote activation of collaborative computing devices and provide indication of devices in use to users present at the device.
Other considerations for remote work security
- Be aware of phishing and social engineering attempts related to IT support practices. With IT operations having to support remote workers using various tools and methods, more opportunistic threats are being seen, mimicking activities such as password resets/expirations, help desk remote access, and 3rd party vendor solution alerts.
- Protect video and teleconference meeting confidentiality. Settings that require sign-in or have unique meeting IDs/codes help to prevent unauthorized parties from listening in to private communications.
Contact Cytellix: [email protected]