The Background on Industry Cybersecurity Standards – NIST, CSET, DFARS

How to best understand the Cybersecurity guidance and volumes of information is an ominous challenge? The foundational cybersecurity work produced by NIST (National Institute for Standards and Technology) is a comprehensive cybersecurity review. Rather than diving too deep in to NIST and the regulatory nature of the definition of classified vs unclassified information and its protection, I will touch on the value of measuring a commercial organizations cybersecurity posture.
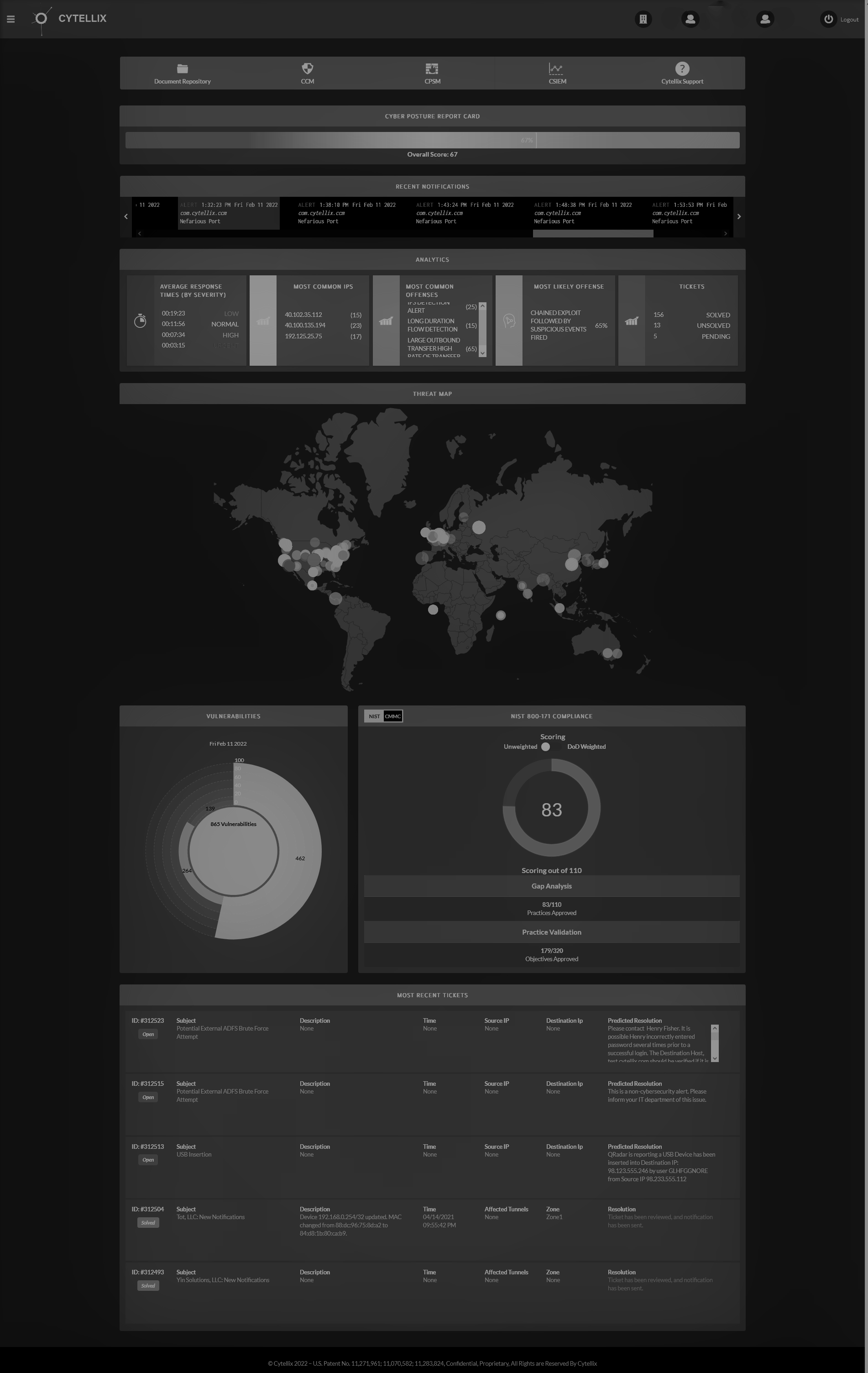
The recommended NIST standards, should you be interested to read, are noted as NIST SP 800-171 http://csrc.nist.gov/publications/drafts/800-171/sp800_171_draft.pdf, published October 18, 2015 identifies a couple very useful tools and premises for measurements. One tool, that is very useful is the CSET (Cyber Security Evaluation Tool) https://cset.inl.gov/SitePages/Home.aspx, which is a self-test, that any organization can use for “free.” While this tool is comprehensive in nature, it does require the user of the tool, to have an in-depth IT and Cyber background to accurately answer the 109 technical questions.
The second very useful part of the NIST publication is the breakdown of measurements into the specific 14-controls: Access Control, Awareness and Training, Auditing and Accountability, Configuration Management, Identification and Authentication, Incident Response, Maintenance, Media Protection, Personnel Security, Physical Protection, Risk Assessment, Security Assessment, System and Communication Protection, System and Information Integrity. By accurately measuring these controls in both a self-test environment (CSET) and using network scanning/situational awareness tools, an organization can get a true grade of their cybersecurity posture to uncover looming vulnerabilities.
The tool (CSET) produces a private result that are defined as a percentage out of 100%, with 100% being equal to compliance. The commercial customer can be measured against a publicly available industry standard, that has been architected to look at a company’s posture without bias. The meaning is to use an industry standard, and by definition, an industry standard is not proprietary. The consulting, technology and solutions market typically use a proprietary methodology to assist in assessments. However, leveraging the standards will give your organization a measurable outcome and baseline for improvements.
Now that we have reviewed the foundations, putting this into practice and having a vision of the effect on your company is an important discussion. Today, any organization, that supplies the federal government with product, solutions or services under a DOD contract, MUST BE COMPLIANT BY 12/31/2017. This date is non-negotiable. Organizations can self-assess or outsource the entire process to cyber experts. There are a few other requirements for compliance beyond providing the 100% System Security Plan, which include a Plan of Action and Milestones (your cyber improvement plan), a gap analysis (what are my company challenges), continuous monitoring and cyber incident reporting processes. The commercial market cyber need is increasing daily, with both compliance, business continuity needs and basic preparedness. The standards approach is a very good methodology and starting place.
Other industries that will see changes for compliance in variations of this standard include: Healthcare, Financial Services, Food Safety, manufacturing and the Small and Medium Businesses (SMB’s). Here are some great references to see where the future of Cybersecurity preparedness is heading.
- DFARS 252.204-7012 referenced as contract language for federal NIST 800-171 - designed for non-federal information systems (commercial)
- NIST 800-53 cybersecurity framework for Federal information systems
- Cybersecurity Framework for critical infrastructure – references NIST 800-53
- Health Care Industry Cybersecurity Task Force recommends NIST Cybersecurity framework