Where are cybersecurity threats coming from?
There has been a lot of recent news and discussion about several malware variants that have been defined as ransomware attacks. There are and have been other damaging malware attacks, but ransomware popularity is currently very well publicized.
Ransomware attacks are not simple but are commonplace in the market today. These attacks typically find their way into an organization through social engineering. To be more specific, the malware is embedded in an attachment as an executable. There are several outcomes from ransomware that we have seen thus far: an individual machine is encrypted and the decryption key is held for ransom by the attacker and a currency request of a “Bitcoin” is requested to decrypt the machine in question. The nastier variants can traverse from machine to machine through the network, creating a systemwide infection. This attack causes severe networkwide shutdowns, causing an organization to recover through more significant ransom payments, or if the company was prepared, backup remediation steps are taken.
The availability of targets for ransomware attacks is almost unlimited, with small and medium businesses (SMBs) being the most vulnerable. Most SMBs are not well-equipped to handle these attacks. There are a few typical dilemmas the SMBs face: What is a bitcoin and how do I get one/them? We did not prepare our network and back-up processes to remediate the problem. Lastly, law enforcement does not recommend payment to the ransom and there is no guarantee that the attacker will actual provide a legitimate decryption key.
The other type of attack—less publicized but equally damaging—is the “insider threat,” wherein the attacker is currently or was previously authorized to work inside your organization. These individuals can cause incalculable damage to your company. As an example, these can be system level attacks or result in losses of intellectual property. The insider threat is as complex to detect and remediate as an external attack. The differentiator here is the insider knows the weaknesses and knows where to find the most valuable information. As with external threats, experts recommend both employee training and monitoring capabilities to detect real-time behavioral changes.
Some additional processes to help SMBs monitor their employees, networks and behaviors to identify insider and external threats include:
- Developing and enforcing policies for access to information systems
- Monitoring and auditing inappropriate access – remediating upon discovery
- Enforcing authentication and limited login attempt processes
- Monitoring printers, downloading (large), queries and email
- Deploying real-time networks monitoring for flow, files, connections, ports and suspicious IPs
- Managing identities of current and past employees


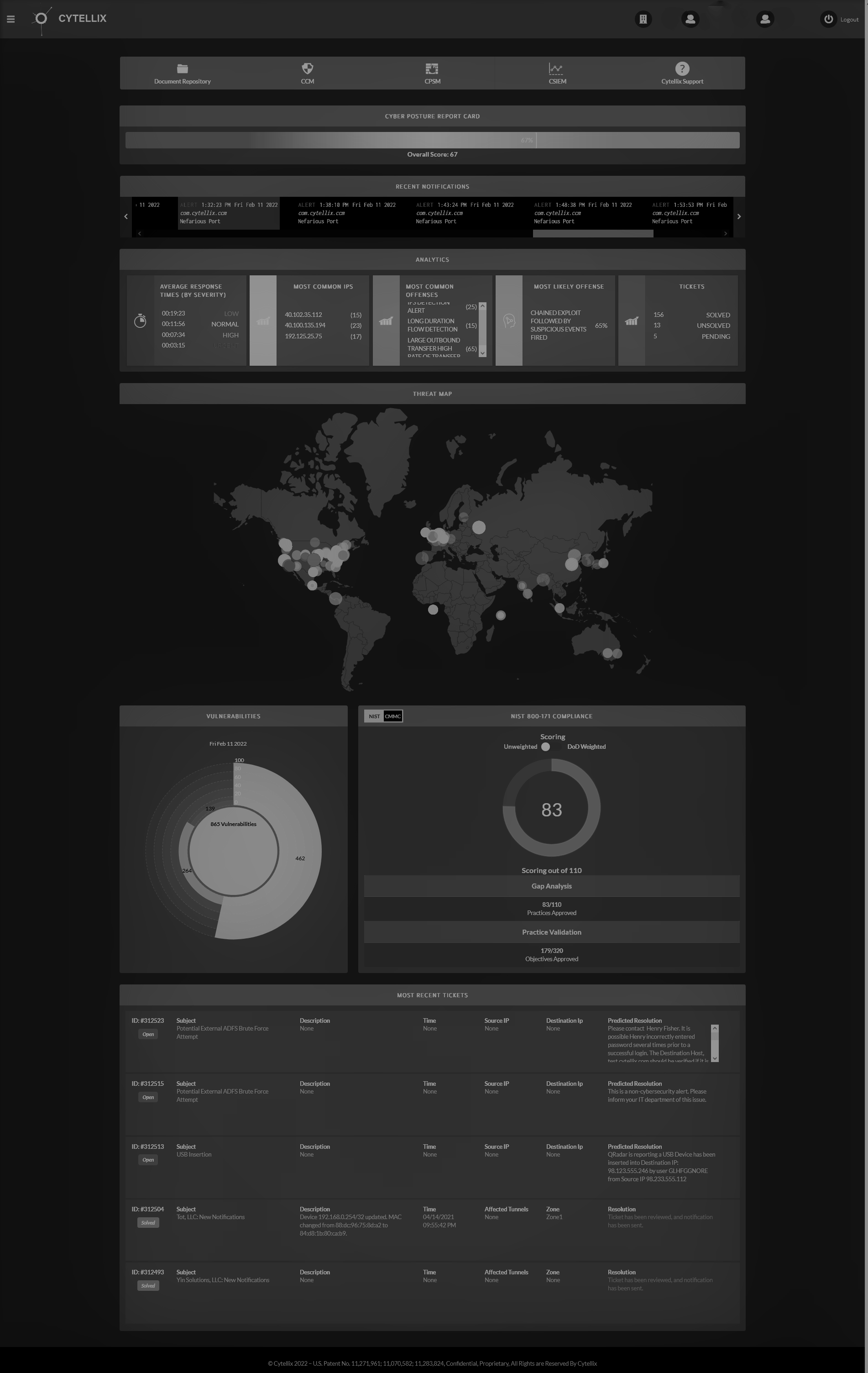
Cytellix® Cyber Watch Platform (C-CWP™)
C-CWP™ provides value by baselining the truth about the true cyber posture of our customers. We then move towards a cybersecurity mesh architecture of integrated continuous improvement that aligns with business objectives. C-CWP™ is an interoperable and open platform designed for change in posture and threat landscape. C-CWP™ is delivered as a complete “turnkey” outsourced service or in combination with internal teams and previously purchased security capabilities

Cytellix® Endpoint Detection Response (C-EDR™)
Cytellix® Endpoint Detection & Response (C-EDR™) is a flexible solution that can be used standalone, enables bring-your-own-license or can be provided turnkey as a complete managed solution with our C-GRC™, C-MDR™, XDR, SOC 24x7x365 managed Turnkey Solutions. The Cytellix turnkey C-EDR™ is a Enterprise grade solution that is complete and has full integration with the Cytellix platform.

Cytellix® Governance Risk & Compliance (C-GRC™) & IT Risk Management (IRM)
Risk Management requirements are evolving to align to the changes arising from compliance risk shifting towards regulatory impact on business process. The demand on organizations to understand their cybersecurity posture, report status and meet regulatory obligations is driving demand across the enterprise (small>large) for a non-technical, turnkey all-inclusive platform.

Cytellix® Managed Detection Response (C-MDR™)
Patented technology compiles information from the vulnerability's, governance, risk, compliance assessments, event data, and analytics. Delivers real-time analysis, including continuous improvement visualization and scorecard.

Extended Detection Response (C-XDR™)
The Cytellix® Extended Detection Response (C-XDR™) solution leverages our flagship Cytellix Cyber Watch Portal (C-CWP™) as turnkey compliance, awareness and response platform. Our C-XDR™ includes, vulnerability management, devices profiling, network segmentation, asset discover, threat intelligence, leak detection, EDR, pre-defined use cases for log ingestion and correlation of threats and our USA based 24x7x365 Security Operations Center (SOC). The Cytellix platform leverages our in-house AI/ML models for real-time telemetry, threat discovery/hunting and ticket reduction. This is a complete turn-key, affordable XDR solution.

Cybersecurity for Small and Medium Business
Cytellix® has designed its platform to enable the small and medium business to adopt quickly, with low friction at an affordable price. We have found that the tasks of both regulatory compliance with cybersecurity frameworks and building a high quality cybersecurity monitoring and infrastructure is a significant time, resource and expense issue for SMB's.
How We're Different
Cytellix® is a first-of-its kind patented SaaS platform that brings together cybersecurity, compliance, and risk management under one fully integrated umbrella. We know your "real security posture" and can provide a new way to manage and deploy cybersecurity capabilities, risk awareness, and compliance with a plan tailored to your specific situation and needs.
Contact Us
- ssdfsThank yo for subscribing.
We will get btackts to you as soon as posTsible.
Oops, there was an error sending your message.
Please try again later.
The Cytellix® team of experts have been delivering cybersecurity for the past 15-years to some of the largest networks in the world. This expertise is delivered to our SMB customers as an affordable, precise, and comprehensive solution designed for organizations who need to comply with Cybersecurity regulatory requirements. There is no other fully integrated GRC, MDR, XDR, EDR single pane of glass solution that is as rich in capabilities, as easy to use and available in production today.
General Inquiries: 1.949.215.8889
Cytellix® - Patent Pending. All Rights are Reserved By Cytellix®




